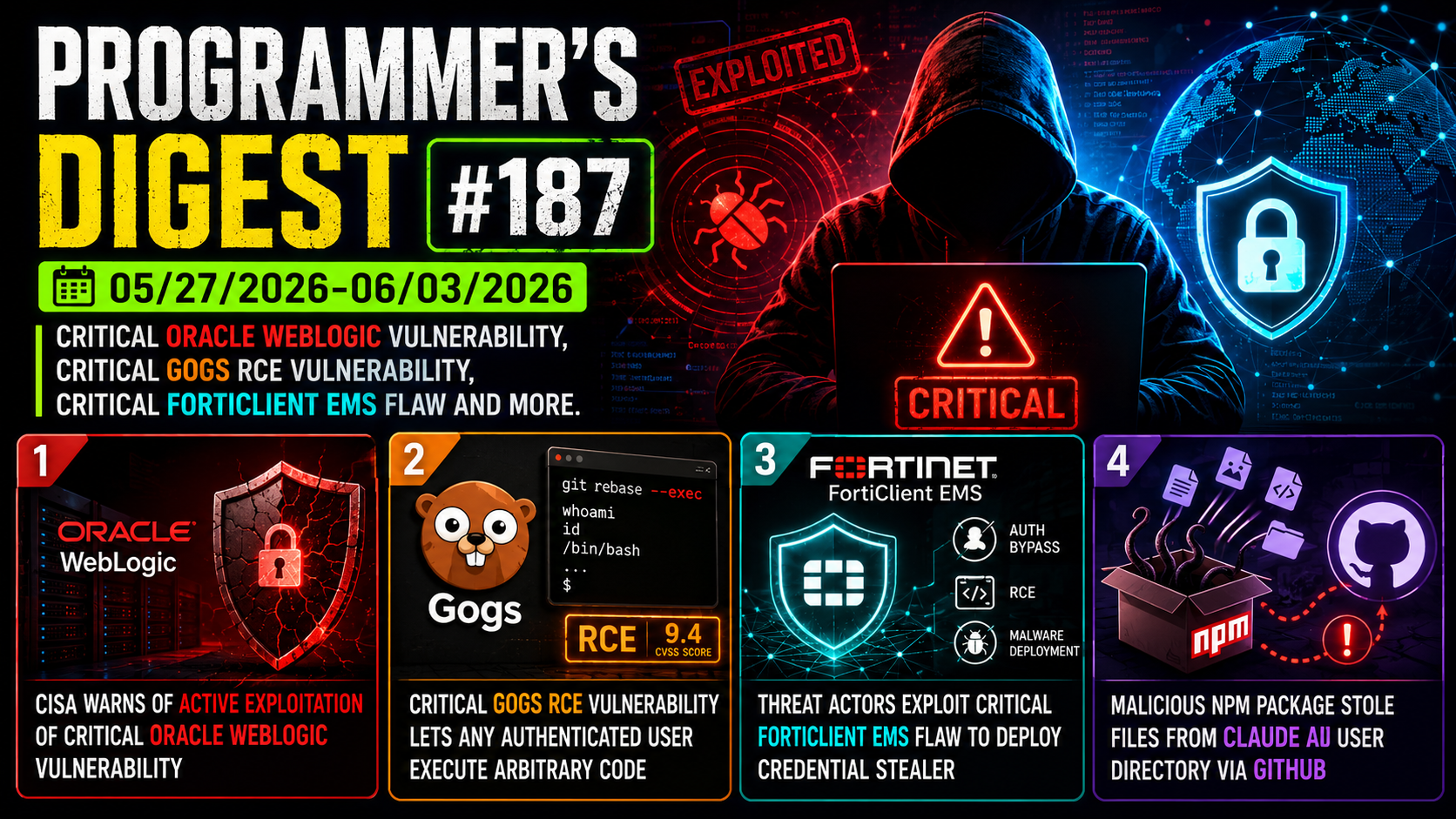
Programmer’s Digest #188
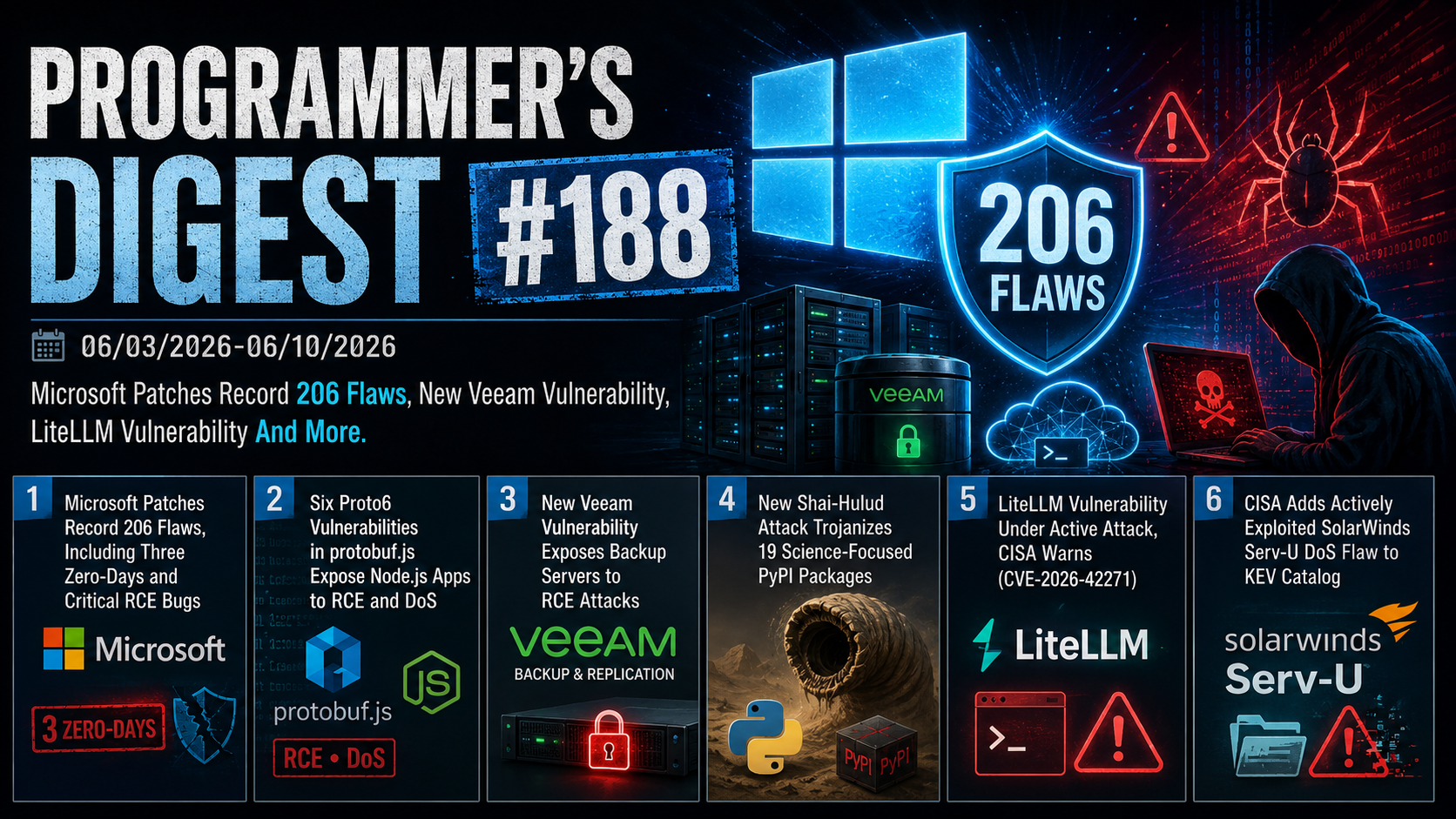
06/03/2026-06/10/2026 Microsoft Patches Record 206 Flaws, New Veeam Vulnerability, LiteLLM Vulnerability And More.
1. Microsoft Patches Record 206 Flaws, Including Three Zero-Days and Critical RCE Bugs
Microsoft’s June 2026 Patch Tuesday addresses a record 206 vulnerabilities — 39 Critical, 167 Important — spanning privilege escalation, RCE, information disclosure, and spoofing flaws, plus two non-Microsoft CVEs and over 350 Chromium fixes bundled with Edge.
The most severe is CVE-2026-45657 (CVSS 9.8), a Windows Kernel use-after-free enabling unauthenticated RCE via malicious TCP/IP traffic. Also critical: CVE-2026-47291 (CVSS 9.8) in HTTP.sys and CVE-2026-44815 (CVSS 9.8), a DHCP Client buffer overflow requiring no credentials or user interaction.
Three publicly disclosed zero-days are patched: CVE-2026-50507 (BitLocker bypass “bitskrieg”), CVE-2026-45586 (CTFMON privilege escalation, linked to “GreenPlasma”), and CVE-2026-49160 (HTTP.sys DoS tied to the HTTP2/Bomb technique, which can exhaust 64 GB RAM in ~45 seconds). The update also fixes “MiniPlasma,” an incomplete patch from December 2020. BitLocker bypass CVE-2026-45585 (“YellowKey”, CVSS 6.8) is additionally addressed.
The record patch volume is attributed to AI-assisted vulnerability discovery, a trend researchers expect to accelerate.
2. Six Proto6 Vulnerabilities in protobuf.js Expose Node.js Apps to RCE and DoS
Six vulnerabilities (collectively “Proto6”) have been discovered in protobuf.js, a JavaScript/TypeScript implementation of Google’s Protocol Buffers serialization library, enabling RCE and DoS attacks against Node.js applications, Google Cloud client libraries, messaging frameworks like Baileys, and CI/CD pipelines.
The six CVEs range from CVSS 5.3 to 8.7:
- CVE-2026-44289/44290 (CVSS 7.5): DoS via unbounded recursion and unsafe option paths
- CVE-2026-44292/44294 (CVSS 5.3): Prototype injection and DoS from crafted field names
- CVE-2026-44291 (CVSS 8.1): Code execution via prototype pollution gadget — the most severe
- CVE-2026-44295 (CVSS 8.7): Code injection in static output from malicious schema names
All flaws stem from the library treating schemas and metadata as trusted by default. CVE-2026-44291 is particularly dangerous: attacker-controlled input can pollute Object.prototype, causing protobuf.js to compile arbitrary JavaScript via Function().
Affected versions: protobufjs ≤7.5.5 / 8.0.0–8.0.1 and protobufjs-cli ≤1.2.0 / 2.0.0–2.0.1. Patches are available in protobufjs 7.5.6/8.0.2 and protobufjs-cli 1.2.1/2.0.2.
3. New Veeam Vulnerability Exposes Backup Servers to RCE Attacks
Veeam has patched CVE-2026-44963 (critical), an RCE vulnerability in Backup & Replication (VBR) affecting all version 12 builds up to 12.3.2.4465, discovered by WatchTowr researcher Sina Kheirkhah. Any authenticated low-privileged domain user can exploit it — but only on domain-joined servers, contrary to Veeam’s own workgroup deployment guidance. Version 13.x is unaffected. The fix is in version 12.3.2.4854.
No active exploitation has been reported, though Veeam warns attackers routinely reverse-engineer patches to target unpatched systems.
VBR is a persistent ransomware target: compromising backup servers enables data theft, lateral movement, and destruction of recovery options. CISA has listed four VBR flaws as actively exploited; Akira, Fog, Frag, Cuba, and FIN7-linked groups have all previously weaponized critical VBR RCE bugs — most recently CVE-2024-40711 in late 2024. Veeam serves 550,000+ customers globally, including 82% of Fortune 500 companies.
4. New Shai-Hulud Attack Trojanizes 19 Science-Focused PyPI Packages
A new wave of the Shai-Hulud supply-chain campaign has compromised 19 PyPI packages — including popular bioinformatics tools Dynamo, Spateo, CoolBox, U-FISH, and Napari-UFISH — across 37 malicious releases, collectively downloaded hundreds of thousands of times.
Discovered by Socket, the attack plants a *-setup.pth file and obfuscated _index.js payload inside compromised wheels. Simply starting Python triggers the PTH file, which downloads the Bun JavaScript runtime from GitHub to execute the script — activating silently during pip installs, test runs, or CI jobs.
The malware targets a broad range of developer secrets: GitHub tokens, npm/PyPI/RubyGems publishing tokens, AWS/GCP/Azure/Kubernetes credentials, SSH keys, Docker credentials, shell histories, and Claude/MCP config files. Exfiltration uses auto-created GitHub repositories; a secondary HTTPS channel mimics an Anthropic API endpoint for camouflage. Persistence is established via systemd (Linux) or LaunchAgents (macOS).
Shai-Hulud’s total attributed artifacts now stand at 453. Affected organizations should rotate all secrets and restore from clean backups.
5. LiteLLM Vulnerability Under Active Attack, CISA Warns (CVE-2026-42271)
CISA has added CVE-2026-42271, a command injection flaw in BerryAI’s LiteLLM AI gateway, to its Known Exploited Vulnerabilities catalog. LiteLLM is a widely used open-source library providing a unified interface for multiple LLM APIs.
The vulnerability, disclosed April 2026, stems from two MCP server test endpoints (POST /mcp-rest/test/connection and POST /mcp-rest/test/tools/list) that accepted full server configurations — including command, args, and env fields — and spawned supplied commands as subprocesses with proxy privileges. Exploitation required only a valid API key with no role check.
The attack bar drops further when chained with CVE-2026-48710 (“BadHost”), an authentication bypass in the Starlette framework that LiteLLM depends on, enabling unauthenticated RCE. Successful exploitation allows arbitrary command execution, credential theft, lateral movement into connected AI infrastructure, and downstream system compromise.
Fixes are available in LiteLLM v1.83.7 and Starlette v1.0.1. CISA has ordered federal agencies to patch by June 22. This marks the second weaponized LiteLLM flaw within a month.
6. CISA Adds Actively Exploited SolarWinds Serv-U DoS Flaw to KEV Catalog
CISA has added CVE-2026-28318 (CVSS 7.5), a denial-of-service vulnerability in SolarWinds Serv-U file server software, to its KEV catalog due to active exploitation.
The flaw is an uncontrolled resource consumption bug: unauthenticated attackers can crash the Serv-U service by sending specially crafted POST requests using Content-Encoding: deflate. No credentials or user interaction are required.
SolarWinds published an advisory this week confirming the issue. CISA’s cataloging indicates the vulnerability is being actively leveraged in the wild, and federal civilian agencies are required to remediate it within the standard KEV deadline. Users are advised to apply available patches immediately.