Programmers’ Digest 21.09.2022-28.09.2022: Critical Vulnurability in Oracle Cloud, GitHub Cybersecurity Breach, Critical Magneto Vulnurability And More
1. Researchers Disclose Critical Vulnerability in Oracle Cloud Infrastructure
Researchers have disclosed a new severe Oracle Cloud Infrastructure (OCI) vulnerability that could be exploited by users to access the virtual disks of other Oracle customers. At its core, the vulnerability is rooted in the fact that a disk could be attached to a compute instance in another account via the Oracle Cloud Identifier (OCID) without any explicit authorization. This meant that an attacker in possession of the OCID could have taken advantage of AttachMe to access any storage volume, resulting in data exposure, exfiltration, or worse, alter boot volumes to gain code execution. Besides knowing the OCID of the target volume, another prerequisite to pull off the attack is that the adversary’s instance must be in the same Availability Domain (AD) as the target.
Insufficient validation of user permissions is a common bug class among cloud service providers. The best way to identify such issues is by performing rigorous code reviews and comprehensive tests for each sensitive API in the development stage.
2. Hackers Stealing GitHub Accounts Using Fake CircleCI Notifications
GitHub is warning of an ongoing phishing campaign that started on September 16 and is targeting its users with emails that impersonate the CircleCI continuous integration and delivery platform.
The bogus messages inform recipients that the user terms and privacy policy have changed and they need to sign into their GitHub account to accept the modifications and keep using the services.
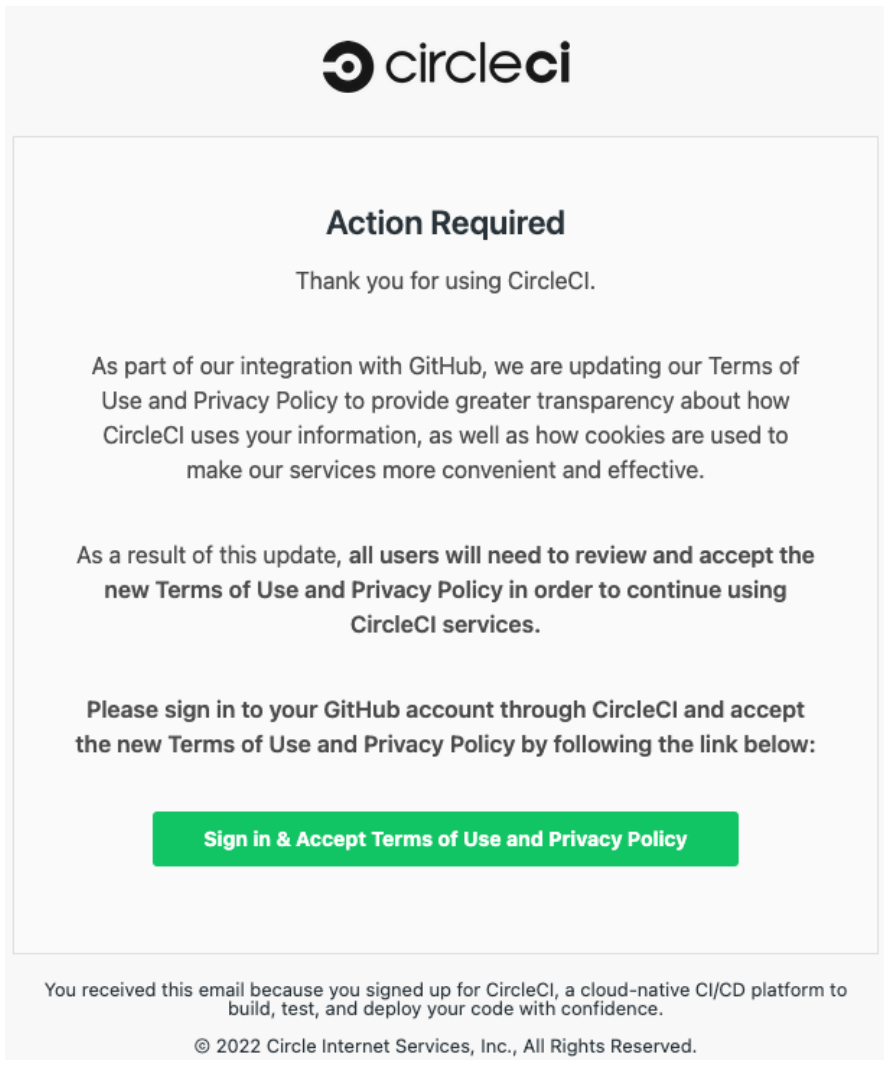
The threat actors’ goal is to steal GitHub account credentials and two-factor authentication (2FA) codes by relaying them through reverse proxies. Accounts protected with hardware security keys for multi-factor authentication (MFA) are not vulnerable to this attack. After obtaining valid account credentials, the threat actors create personal access tokens (PATs), authorize OAuth apps, and sometimes add SSH keys to the account to persist even after a password reset. If you haven’t received a notice from GitHub but have valid grounds to believe you may be a victim of the phishing campaign, the recommendation is to reset your account password and 2FA recovery codes, review your PATs, and, if possible, start using a hardware MFA key.
3. Lessons From the GitHub Cybersecurity Breach
When GitHub revealed details about a security breach that allowed an unknown attacker to download data from dozens of private code repositories, it was a nightmare scenario. Attackers were using information collected from GitHub to target two third-party cloud platforms-as-a-service (PaaS): Heroku and Travis CI. Attackers had stolen OAuth tokens issued to Heroku and Travis CI and used them to access and download the contents of private repositories.
These three simple steps can help improve cybersecurity posture on Salesforce.
- Use Salesforce-Native Applications. Applications built on Salesforce ensure that your data remains in one place with the same cybersecurity posture as the Salesforce platform. With apps consolidated on a single platform, the attack surface is greatly reduced.
- Establish a Zero-Trust Model. Never trust, always verify. All users should have the minimum level of permissions and access needed to be able to complete their necessary tasks while requiring users to prove their need and identities before access. Audit everything.
- Utilize Secrets Management. Never store credentials in clear text, and always assume private repositories are public. Having a secrets management solution ensures that your secrets are rotated along with having an appropriate level of security compliance around your credentials.
With this improved cybersecurity posture, developers, infosec teams, and the CEO will be at ease knowing that the organization’s most sensitive data is secure.
4. Critical Magento Vulnerability Targeted in New Surge of Attacks
Researchers have observed a surge in hacking attempts targeting CVE-2022-24086, a critical Magento 2 vulnerability allowing unauthenticated attackers to execute code on unpatched sites. Magento is an open-source e-commerce platform owned by Adobe, used by approximately 170,000 online shopping websites worldwide. The CVE-2022-24086 vulnerability was discovered and patched in February 2022, when threat actors were already exploiting it in the wild. At the time, CISA published an alert urging site admins to apply the available security update.
A couple of days later, security researchers published a proof-of-concept (PoC) exploit for CVE-2022-24086, opening the road to mass exploitation.
According to a report published by Sansec today, we have reached that stage, with the critical template vulnerability becoming a favorite in the hacker underground. Sansec’s analysts have observed three attack variants exploiting CVE-2022-24086 to inject a remote access trojan (RAT) on vulnerable endpoints.
5. CISA Warns of Critical ManageEngine RCE Bug Used in Attack
The Cybersecurity and Infrastructure Security Agency (CISA) has added a critical severity Java deserialization vulnerability affecting multiple Zoho ManageEngine products to its catalog of bugs exploited in the wild. This security flaw (CVE-2022-35405) can be exploited in low-complexity attacks, without requiring user interaction, to gain remote code execution on servers running unpatched Zoho ManageEngine PAM360 and Password Manager Pro (without authentication) or Access Manager Plus (with authentication) software.
After being added to CISA’s Known Exploited Vulnerabilities (KEV) catalog, all Federal Civilian Executive Branch Agencies (FCEB) agencies now must patch their systems against this bug exploited in the wild according to a binding operational directive (BOD 22-01) issued in November. The federal agencies have three weeks, until October 13th, to ensure that their networks are protected from exploitation attempts.
6. Npm Packages Used by Crypto Exchanges Compromised
Multiple npm packages published by the crypto exchange, dYdX, and used by at least 44 cryptocurrency projects appear to have been compromised. The packages in question, shown below, appear to have been published from the npm account of a dYdX crypto platform employee, BleepingComputer observed, although the exact cause of this compromise is yet to be determined:
1. @dydxprotocol/solo – versions 0.41.1, 0.41.2
2. @dydxprotocol/perpetual – versions 1.2.2, 1.2.3
An earlier advisory claimed that the package ‘@dydxprotocol/node-service-base-dev’ was also affected but it has since been withdrawn.
BleepingComputer observed the compromised version 0.41.1 of ‘solo’ package was still live on npm at the time of writing. These packages make up the “Ethereum Smart Contracts and TypeScript library used for the dYdX Solo Trading Protocol.”
The solo package, for example, is used by at least 44 GitHub repositories belonging to multiple crypto platforms. GitHub READMEs for both ‘solo’ and ‘perpetual’ state these are being “currently used by trade.dydx.exchange.”
7. Native Function and Assembly Code Invocation
For a reverse engineer, the ability to directly call a function from the analyzed binary can be a shortcut that bypasses a lot of grief. While in some cases it is just possible to understand the function logic and reimplement it in a higher-level language, this is not always feasible.
In the article, you will learn about 3 different ways to make this “shortcut” happen, and invoke functions directly from assembly.
The article first covers the IDA Appcall feature which is natively supported by IDA Pro, and can be used directly using IDAPython.
Then it demonstrates how to achieve the same feat using Dumpulator;
and finally, you will learn how to get that result using emulation with Unicorn Engine. The practical example used in this article is based on the “tweaked” SHA1 hashing algorithm implemented by a sample of the MiniDuke malware.
8. Hackers Exploited Zero-Day RCE Vulnerability in Sophos Firewall — Patch Released
Security software company Sophos has released a patch update for its firewall product after it was discovered that attackers were exploiting a new critical zero-day vulnerability to attack its customers’ network.
The issue, tracked as CVE-2022-3236 (CVSS score: 9.8), impacts Sophos Firewall v19.0 MR1 (19.0.1) and older and concerns a code injection vulnerability in the User Portal and Webadmin components that could result in remote code execution.
As a workaround, Sophos is recommending that users take steps to ensure that the User Portal and Webadmin are not exposed to WAN. Alternatively, users can update to the latest supported version: v19.5 GA; v19.0 MR2 (19.0.2); v19.0 GA, MR1, and MR1-1; v18.5 MR5 (18.5.5); v18.5 GA, MR1, MR1-1, MR2, MR3, and MR4.
