Programmers’ Digest #07
1. Nighthawk Likely to Become Hackers’ New Post-Exploitation Tool After Cobalt Strike
A nascent and legitimate penetration testing framework known as Nighthawk is likely to gain threat actors’ attention for its Cobalt Strike-like capabilities. Enterprise security firm Proofpoint said it detected the use of the software in mid-September 2022 with a number of test emails sent using generic subject lines such as “Just checking in” and “Hope this works2.” The email messages contained booby-trapped URLs, which, when clicked, redirected the recipients to an ISO image file containing the Nighthawk loader. The obfuscated loader comes with the encrypted Nighthawk payload, a C++-based DLL that uses an elaborate set of features to counter detection and fly under the radar. Of particular note are mechanisms that can prevent endpoint detection solutions from being alerted about newly loaded DLLs in the current process and evade process memory scans by implementing a self-encryption mode.
2. Atlassian Releases Patches for Critical Flaws Affecting Crowd and Bitbucket Products
Australian software company Atlassian has rolled out security updates to address two critical flaws affecting Bitbucket Server, Data Center, and Crowd products. The issues, tracked as CVE-2022-43781 and CVE-2022-43782, are both rated 9 out of 10 on the CVSS vulnerability scoring system. CVE-2022-43781, which Atlassian said was introduced in version 7.0.0 of Bitbucket Server and Data Center, affects versions 7.0 to 7.21 and 8.0 to 8.4. The weakness has been described as a case of command injection using environment variables in the software, which could allow an adversary with permission to control their username to gain code execution on the affected system. As a temporary workaround, the company is recommending users turn off the “Public Signup” option (Administration > Authentication).
The second vulnerability, CVE-2022-43782, concerns a misconfiguration in Crowd Server and Data Center that could permit an attacker to invoke privileged API endpoints, but only in scenarios where the bad actor is connecting from an IP address added to the Remote Address configuration. Introduced in Crowd 3.0.0 and identified during an internal security review, the shortcoming impacts all new installations, meaning users who upgraded from a version prior to Crowd 3.0.0 are not vulnerable.
3. W4SP Stealer Constantly Targeting Python Developers in Ongoing Supply Chain Attack
An ongoing supply chain attack has been leveraging malicious Python packages to distribute malware called W4SP Stealer, with over hundreds of victims ensnared to date. The threat actor is still active and is releasing more malicious packages.The attack seems related to cybercrime as the attacker claims that these tools are undetectable to increase sales.The findings from Checkmarx build on recent reports from Phylum and Check Point, which flagged 30 different modules published on the Python Package Index (PyPI) that were designed to propagate malicious code under the guise of benign-looking packages.
The attack is just the latest threat to target the software supply chain. What makes it notable is the use of steganography to extract a polymorphic malware payload hidden within an image file hosted on Imgur.
The installation of the package ultimately makes way for W4SP Stealer (aka WASP Stealer), an information stealer engineered to exfiltrate Discord accounts, passwords, crypto wallets, and other files of interest to a Discord Webhook.
4. Researchers Discover Hundreds of Amazon RDS Instances Leaking Users’ Personal Data
Hundreds of databases on Amazon Relational Database Service (Amazon RDS) are exposing personal identifiable information (PII), as new findings from Mitiga, a cloud incident response company, show. Leaking PII in this manner provides a potential treasure trove for threat actors – either during the reconnaissance phase of the cyber kill chain or extortionware/ransomware campaigns.
The root cause of the leaks stems from a feature called public RDS snapshots, which allows for creating a backup of the entire database environment running in the cloud and can be accessed by all AWS accounts.
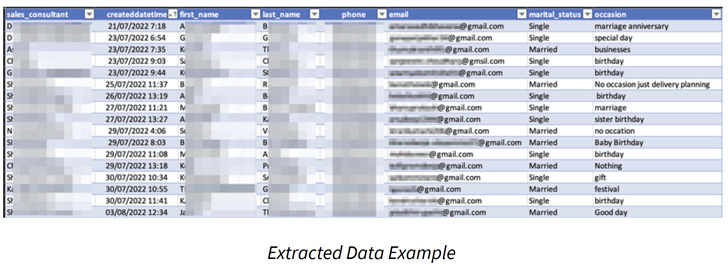
Of the 810 snapshots, over 250 of the backups were exposed for 30 days, suggesting that they were likely forgotten. Based on the nature of the information exposed, adversaries could either steal the data for financial gain or leverage it to get a better grasp of a company’s IT environment, which could then act as a stepping stone for covert intelligence gathering efforts.
Recommendation
It’s highly recommended that RDS snapshots are not publicly accessible in order to prevent potential leak or misuse of sensitive data or any other kind of security threat.
5. Exploit Released for Actively Abused ProxyNotShell Exchange Bug
Proof-of-concept exploit code has been released online for two actively exploited and high-severity vulnerabilities in Microsoft Exchange, collectively known as ProxyNotShell. Tracked as CVE-2022-41082 and CVE-2022-41040, the two bugs affect Microsoft Exchange Server 2013, 2016, and 2019 and allow attackers to escalate privileges to run PowerShell in the context of the system and gain arbitrary or remote code execution on compromised servers. Microsoft released security updates to address the two security flaws as part of the November 2022 Patch Tuesday.
One week after Microsoft released ProxyNotShell security updates, security researcher Janggggg released the proof-of-concept (PoC) exploit attackers have used in the wild to backdoor Exchange servers. Attackers have been chaining the two security flaws to deploy Chinese Chopper web shells on compromised servers for persistence and data theft, as well as for lateral movement in their victims’ networks since at least September 2022.
6. This Malware Installs Malicious Browser Extensions to Steal Users’ Passwords and Cryptos
A malicious extension for Chromium-based web browsers has been observed to be distributed via a long-standing Windows information stealer called ViperSoftX. Czech-based cybersecurity company dubbed the rogue browser add-on VenomSoftX owing to its standalone features that enable it to access website visits, steal credentials and clipboard data, and even swap cryptocurrency addresses via an adversary-in-the-middle (AiTM) attack. This multi-stage stealer exhibits interesting hiding capabilities, concealed as small PowerShell scripts on a single line in the middle of otherwise innocent-looking large log files, among others. ViperSoftX focuses on stealing cryptocurrencies, clipboard swapping, fingerprinting the infected machine, as well as downloading and executing arbitrary additional payloads, or executing commands.
The distribution vector used to propagate ViperSoftX is typically done by means of cracked software for Adobe Illustrator and Microsoft Office that are hosted on file-sharing sites. The downloaded executable file comes with a clean version of cracked software along with additional files that set up persistence on the host and harbor the ViperSoftX PowerShell script. Avast said it has detected and blocked over 93,000 infections since the start of 2022, with a majority of the impacted users located in India, the U.S., Italy, Brazil, the U.K., Canada, France, Pakistan, and South Africa.
