Programmer’s Digest #182
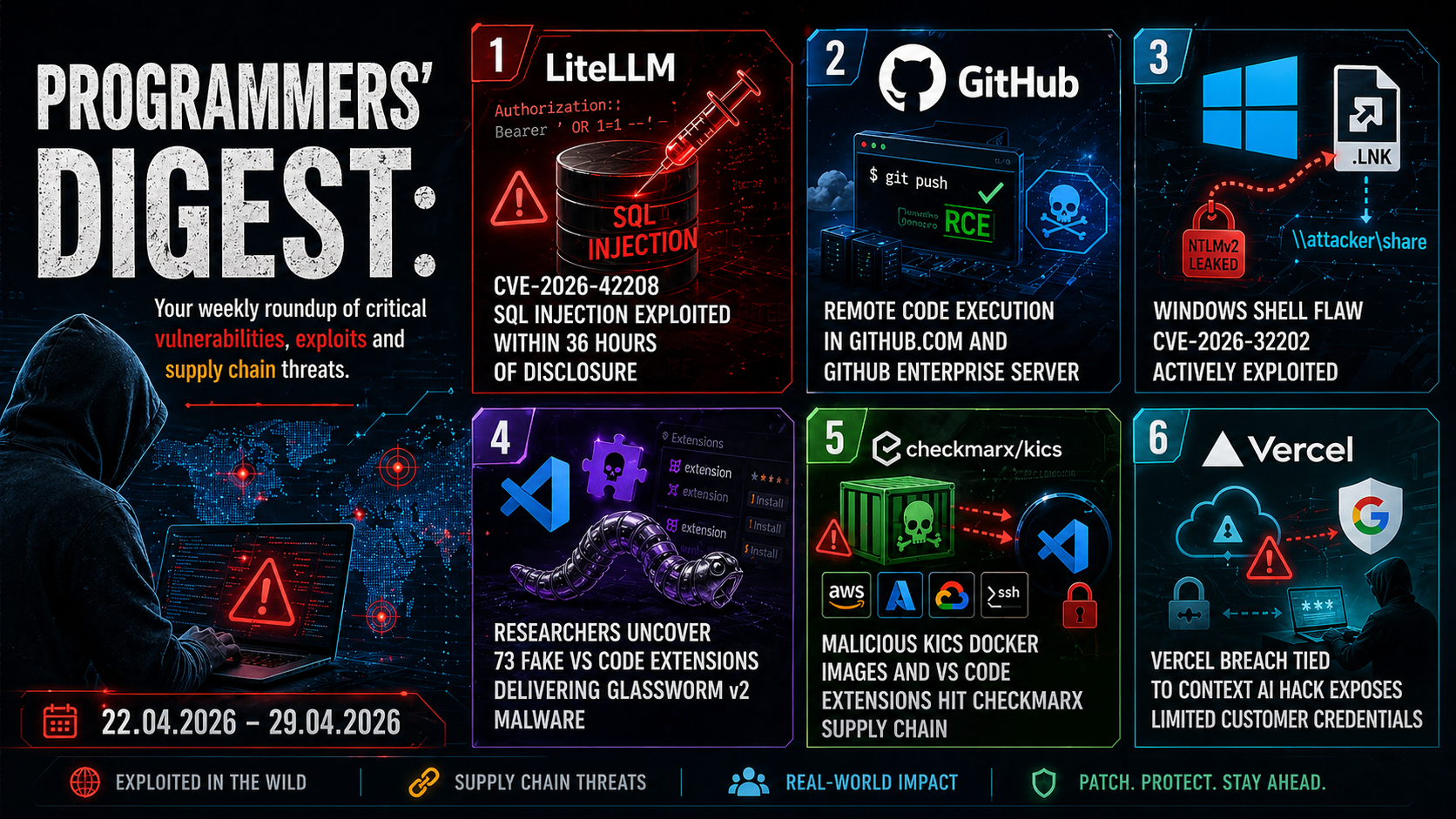
04/22/2026-04/29/2026 LiteLLM CVE-2026-42208 SQL Injection Exploited, Windows Shell Flaw CVE-2026-32202, Malicious KICS Docker Images And More.
1. LiteLLM CVE-2026-42208 SQL Injection Exploited within 36 Hours of Disclosure
A critical flaw in LiteLLM was exploited in the wild within 36 hours of disclosure, highlighting how quickly attackers act. The vulnerability, CVE-2026-42208 (CVSS 9.3), is an SQL injection that lets unauthenticated attackers manipulate the LiteLLM proxy database. By sending a crafted Authorization header, attackers could access sensitive data, including API keys and credentials, and potentially modify them. The issue affects versions ≥1.81.16 and <1.83.7 and was patched in version 1.83.7-stable on April 19, 2026. Exploitation began about 26 hours after public disclosure, with activity traced to specific IP addresses and targeting key database tables holding LLM provider credentials.
Researchers noted attackers focused on high-value secrets rather than user data, suggesting prior knowledge of the schema. Given LiteLLM’s role in managing cloud credentials, a breach could resemble a full cloud compromise. Users are strongly urged to update immediately or disable error logging as a temporary mitigation.
2. Securing GitHub: Wiz Research uncovers Remote Code Execution in GitHub.com and GitHub Enterprise Server
Researchers at Wiz discovered a critical flaw in GitHub’s infrastructure (CVE-2026-3854) that allowed remote code execution using a single git push. The bug stemmed from an injection issue in an internal protocol, letting authenticated users run arbitrary commands on backend servers.
On GitHub.com, attackers could access shared storage nodes containing millions of repositories. On GitHub Enterprise Server, the impact was more severe, enabling full server compromise and access to all repositories and secrets.
The flaw was easy to exploit and was identified using AI-assisted reverse engineering, marking a shift in vulnerability discovery. GitHub fixed the issue on GitHub.com within six hours and released patches for Enterprise Server. However, about 88% of Enterprise instances remained unpatched at the time.
Users of GitHub.com need no action, but Enterprise Server administrators should urgently upgrade to version 3.19.3 or later to mitigate the risk.
3. Windows Shell Flaw CVE-2026-32202 Actively Exploited
Microsoft has confirmed active exploitation of a Windows Shell vulnerability, CVE-2026-32202, raising concerns about patch gaps and evolving cyber threats. Initially addressed in April’s Patch Tuesday, the flaw was later acknowledged as exploited in real-world attacks, increasing its risk profile despite a modest CVSS score of 4.3.
The issue stems from a protection mechanism failure enabling spoofing over a network. Attackers must trick users into opening malicious files, potentially exposing sensitive data without altering systems—making it useful in targeted, stealthy campaigns.
Researchers link this flaw to earlier high-severity vulnerabilities (CVE-2026-21510 and CVE-2026-21513), previously exploited by the state-backed group APT28. The newer flaw appears to be an incomplete fix of earlier issues.
Attacks use malicious Windows shortcut (LNK) files and UNC paths to trigger SMB connections, leaking hashed credentials (Net-NTLMv2) with little user awareness.
The case highlights how partial patches and low-severity flaws can still enable sophisticated, multi-stage attacks, emphasizing the need for timely updates and stronger monitoring.
4. Researchers Uncover 73 Fake VS Code Extensions Delivering GlassWorm v2 Malware
Cybersecurity researchers have identified a campaign, GlassWorm v2, involving 73 malicious Microsoft VS Code extensions on the Open VSX repository. These extensions mimic legitimate ones, copying names, icons, and descriptions to deceive developers. Six are confirmed malicious, while others act as sleeper packages, gaining trust before delivering harmful updates.
First published earlier this month, the campaign has produced over 320 artifacts since December 2025. It relies on social engineering and typosquatting to boost installs, then deploys malware through updates. The extensions function as loaders, fetching a second-stage malicious VSIX extension from GitHub. This payload installs across multiple IDEs, including VS Code, Cursor, Windsurf, and VSCodium. The malware steals sensitive data, installs a remote access trojan (RAT), and deploys a rogue Chromium-based browser extension to capture credentials and other information. It also avoids infecting Russian systems.
The campaign highlights evolving tactics, including obfuscated JavaScript loaders and stealthy multi-stage attacks designed to evade detection.
5. Malicious KICS Docker Images and VS Code Extensions Hit Checkmarx Supply Chain
Cybersecurity researchers warn that malicious images were uploaded to the official Checkmarx “checkmarx/kics” Docker Hub repository. Attackers overwrote legitimate tags (e. g., v2.1.20, alpine) and added a fake v2.1.21 release. The poisoned images contained a modified KICS binary capable of collecting sensitive scan data, encrypting it, and exfiltrating it to an external server. Compromised Visual Studio Code extensions (e. g., cx-dev-assist and ast-results) also delivered malware that downloaded a hidden addon (“mcpAddon.js”) to steal credentials. Stolen data included GitHub tokens, cloud credentials (AWS, Azure, Google Cloud), SSH keys, and environment variables. The malware could also create GitHub repositories, inject malicious workflows, and spread through npm packages. The campaign shows a broader supply chain attack, possibly linked to TeamPCP. Developers using affected tools should assume compromise, remove them, rotate credentials, and audit systems immediately.
6. Vercel Breach Tied to Context AI Hack Exposes Limited Customer Credentials
Web infrastructure provider Vercel has disclosed a breach that allowed attackers to access certain internal systems after compromising Context.ai, a third-party tool used by an employee. The attacker hijacked the employee’s Google Workspace account, gaining access to some environments and non-sensitive variables. Encrypted sensitive data appears unaffected.
A limited number of customers had credentials exposed, and Vercel urged immediate rotation. The company is working with Mandiant and law enforcement to investigate. A group calling itself ShinyHunters claimed responsibility, though this may be disputed.
The breach likely involved stolen OAuth tokens, possibly linked to earlier malware infections. Attackers used these tokens to move laterally into Vercel’s systems.
The incident highlights growing risks in SaaS supply chains, where compromised OAuth credentials enable widespread access. Vercel has since introduced stronger safeguards and monitoring, urging users to enable multi-factor authentication and audit activity logs.
