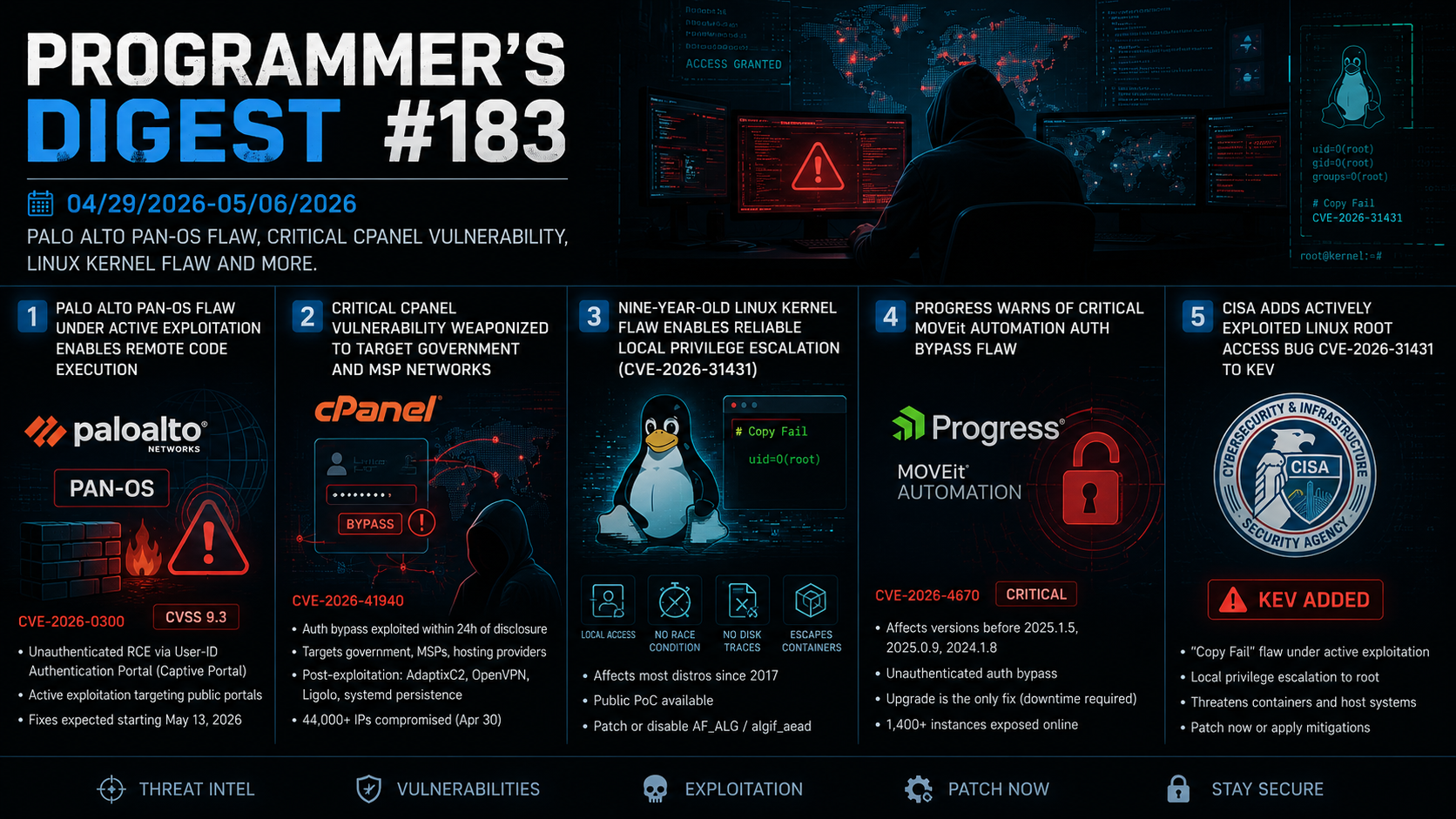
Programmer’s Digest #184
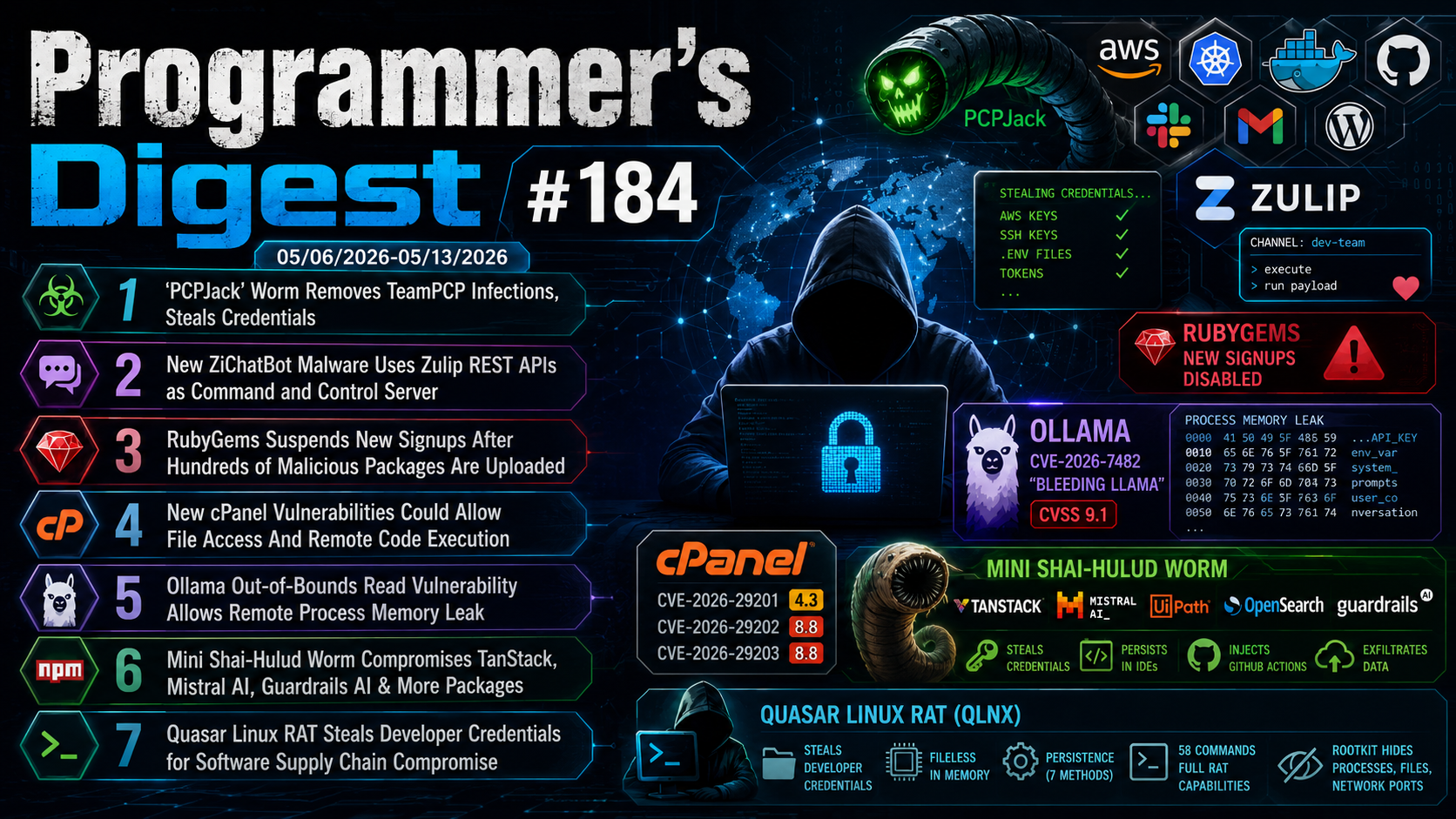
05/06/2026-05/13/2026 PCPJack’ Worm Removes TeamPCP Infections, New ZiChatBot Malware, Ollama Out-of-Bounds Read Vulnerability And More.
1. ‘PCPJack’ Worm Removes TeamPCP Infections, Steals Credentials
A threat actor has launched a campaign to evict the TeamPCP hacking group from infected environments and deploy its own malicious tools. Active since late April, the campaign uses a malware framework called PCPJack that targets credentials across multiple cloud environments and can self-propagate. It begins with a Linux shell script that scans for and removes TeamPCP artifacts, then sets up a Python environment, downloads six modules from an AWS S3 bucket, establishes persistence, and deletes itself. PCPJack steals credentials, SSH keys, .env files, and tokens for services including AWS, Kubernetes, Docker, Gmail, GitHub, Slack, and WordPress. It performs lateral movement, conducts internet-wide scanning via Common Crawl data, and exploits several known CVEs to spread further. Command-and-control is handled via Telegram.
SentinelOne also identified a second toolset linked to the same actor, targeting dozens of additional cloud services. Both toolsets are well-developed and modular, though the actor left Telegram credentials unencrypted — a notable operational security lapse.
2. New ZiChatBot Malware Uses Zulip REST APIs as Command and Control Server
Researchers have discovered ZiChatBot, a cross-platform malware that uses Zulip’s legitimate REST API for command-and-control, allowing it to blend malicious traffic with normal developer communications. Rather than contacting a suspicious private server, it routes commands through a legitimate chat platform — making it harder to detect via standard network monitoring. The malware was distributed through three fake PyPI packages — uuid32-utils, colorinal, and termncolor — designed to mimic common developer libraries. Once installed, they silently dropped the ZiChatBot payload. Kaspersky analysts noted a 64% code similarity between ZiChatBot’s dropper and tooling linked to OceanLotus (APT32), suggesting possible attribution.
ZiChatBot exfiltrates system data and executes shellcode received via Zulip channel messages, signaling completion with a heart emoji. On Windows it persists via a registry entry; on Linux via crontab. The malicious PyPI packages have since been removed and the attacker’s Zulip organization deactivated, though already-infected systems may still attempt contact.
3. RubyGems Suspends New Signups After Hundreds of Malicious Packages Are Uploaded
RubyGems, the official package manager for Ruby, has temporarily stopped new account registrations after a major malicious attack. The attack involved hundreds of packages, mostly targeting Mend.io, with some containing exploits. Visitors to the RubyGems sign-up page now see a notice stating that new account registration has been disabled temporarily. Mend.io, which helps secure RubyGems, said more details will be shared once the situation is under control. The attackers have not yet been identified.
The incident highlights the growing threat of software supply chain attacks on open-source ecosystems. Cybercriminal groups have increasingly compromised popular packages to spread credential-stealing malware, steal sensitive data, and expand attacks.
4. New cPanel Vulnerabilities Could Allow File Access And Remote Code Execution
cPanel has patched three vulnerabilities in cPanel & WHM that could allow file reads, arbitrary code execution, and privilege escalation. The three flaws are: CVE-2026-29201 (CVSS 4.3), an input validation issue enabling arbitrary file reads; CVE-2026-29202 (CVSS 8.8), improper validation in the create_user API allowing authenticated attackers to execute arbitrary Perl code; and CVE-2026-29203 (CVSS 8.8), unsafe symlink handling that could let users manipulate file permissions via chmod, potentially enabling privilege escalation or denial-of-service. Fixes are available across versions 11.136.0.9, 11.134.0.25, 11.132.0.31, and newer builds. No active exploitation of these three flaws has been reported, though the disclosure follows closely on the heels of CVE-2026-41940 — a critical authentication bypass (CVSS 9.3) already added to CISA’s KEV catalog and actively used to deploy Mirai botnet variants.
5. Ollama Out-of-Bounds Read Vulnerability Allows Remote Process Memory Leak
Cybersecurity researchers have disclosed a critical vulnerability in Ollama that could let remote attackers leak sensitive process memory from exposed servers. The flaw, tracked as CVE-2026-7482 and nicknamed “Bleeding Llama,” affects Ollama before version 0.17.1 and has a CVSS score of 9.1. Researchers estimate more than 300,000 servers may be exposed. The issue stems from an out-of-bounds read vulnerability in Ollama’s GGUF model loader. By uploading a specially crafted GGUF file through the /api/create endpoint, attackers can force the server to read beyond allocated memory and potentially steal API keys, environment variables, system prompts, and user conversations. The stolen data can then be exfiltrated using the /api/push endpoint.
Researchers also uncovered two unpatched Windows update flaws that can enable persistent code execution. Users are urged to update Ollama, restrict network exposure, disable automatic updates, and secure instances behind authentication proxies and firewalls.
6. Mini Shai-Hulud Worm Compromises TanStack, Mistral AI, Guardrails AI & More Packages
TeamPCP, the threat group behind recent supply chain attacks, has been linked to a new “Mini Shai-Hulud” campaign targeting npm and PyPI packages tied to TanStack, Mistral AI, UiPath, OpenSearch, and Guardrails AI. More than 170 compromised packages with over 518 million downloads were affected.
The malicious packages contained obfuscated JavaScript malware designed to steal credentials from cloud providers, cryptocurrency wallets, AI tools, GitHub Actions, and developer environments. The malware also established persistence in IDEs like VS Code and Claude Code, injected malicious GitHub Actions workflows, and exfiltrated stolen data through multiple channels. Researchers said the attackers abused GitHub Actions and trusted publishing workflows to distribute validly signed malicious packages, marking one of the first known npm worms with legitimate SLSA Level 3 attestations. Some variants also included destructive “wiper” behavior that could erase developer systems if malicious npm tokens were revoked improperly.
7. Quasar Linux RAT Steals Developer Credentials for Software Supply Chain Compromise
Trend Micro researchers have uncovered a previously undocumented Linux implant called Quasar Linux RAT (QLNX), designed to silently compromise developer environments and enable extensive post-exploitation activity.
QLNX specifically targets supply chain credentials, harvesting secrets from files such as .npmrc, .pypirc, .aws/credentials, .kube/config, GitHub CLI tokens, and .env files — giving attackers potential access to NPM/PyPI publishing pipelines, cloud infrastructure, and CI/CD systems.
The implant runs fileless from memory, disguises itself as a kernel thread, wipes system logs, and establishes persistence via up to seven methods including systemd, crontab, and .bashrc injection. It supports 58 commands covering shell execution, file management, keylogging, screenshots, SOCKS proxying, and P2P mesh networking. A PAM hook backdoor intercepts plaintext credentials during authentication events.
QLNX employs a two-tiered rootkit: a userland component using LD_PRELOAD and a kernel-level eBPF module that hides processes, files, and network ports from standard tools. Its delivery method remains unknown.